
Employee Spotlight: Becca Green
It's our pleasure to spotlight our new Employee of the Quarter, Becca Green! Becca, a proud native of Bradley County, Arkansas, is as vibrant and dynamic as the tall pines and pink tomatoes that her hometown is known for. Having attended the University of Arkansas at Monticello, she majored in Environmental Science, but fate led her to a...

Consultants
Consultant of the Month: Rosemary Lopez
We are excited to celebrate March's Consultant of the Month, Rosemary Lopez! 🎉 Originally from the city that never sleeps, New York, NY, Rosemary has currently made her home in vibrant Jacksonville, Florida. Her journey is marked by various interests and a commitment to excellence, making her an important part of our team. Her care...

Kavaliro News
Kavaliro Sells Salesforce Division to Accordion in Strategic Move to Focus on Core Services
The Sale Will Allow Kavaliro to Expand Its Growing Workforce Solutions and Federal Defense Businesses ORLANDO, Fla., March 10, 2025 -- Kavaliro, a leader in providing innovative technology solutions, is pleased to announce the sale of its Salesforce Division to Accordion, a premier provider of business consulting services. This move is part ...
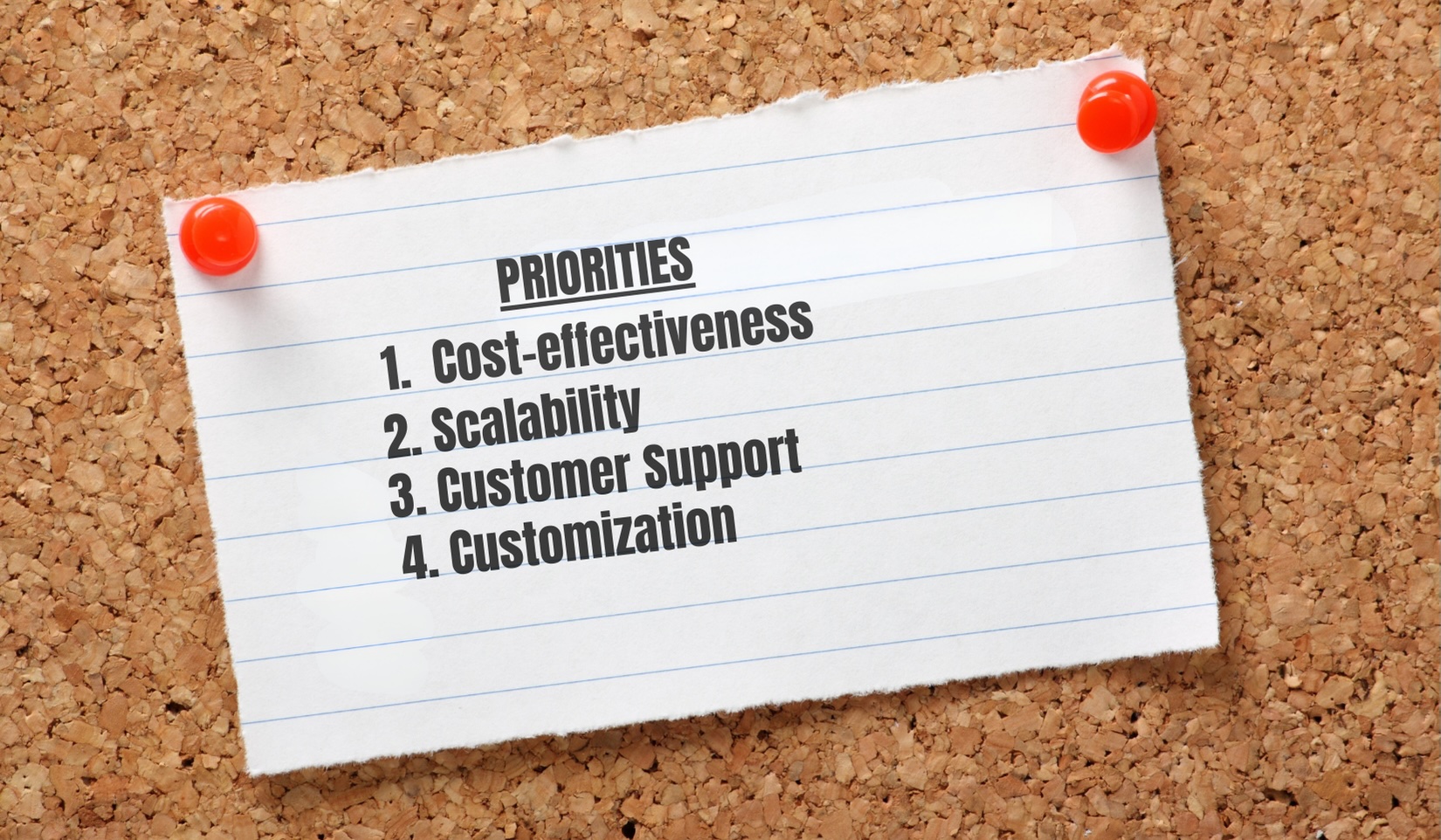
How Kavaliro Exceeds Your Top Priorities In An IT or Workforce Solution Provider
We recently conducted a LinkedIn poll to understand what clients prioritize when choosing an IT or Workforce Solution provider. The results are in, and they help create a clear picture of your needs - needs that, we’re pleased to say, Kavaliro meets consistently and effectively. 1. Cost-effectiveness (41%): Your dollar carries weight and a...

Consultants
Consultants of the Month: Joshua Allen & Tony Panganiban
We are delighted to shine the spotlight on not one, but TWO of our amazing consultants for February Joshua Allen and Tony Panganiban! 🎉 Joshua Allen: Spending his formative years as a part of a vibrant Coast Guard family, Joshua relocated frequently due to the nature of military life. After a while, he and his family ended up in Co...

Kavaliro News
Kavaliro Conference 2025: “The Magic of Possibility”
This past week marked a milestone for the Kavaliro team as we celebrated our 15th annual team conference at the Swan and Dolphin Hotel in Orlando, FL. The event brought many together to participate in our annual conference. Embracing the theme, “The Magic of Possibility", we highlighted the limitless opportunities that lie ahead in our journey of...
How AI and Automation are Reshaping IT Services
In the fast-paced world of technology, the role of Artificial Intelligence (AI) and automation is rapidly transforming the IT services landscape. For companies like ours, these advancements are not just reshaping how services are delivered but are also opening up new opportunities for innovation, efficiency, and growth. Let’s explore the key ways...

Newsletter
Kavaliro Newsletter – 2024 Q4 Wrap Up
2024 was a record-breaking year for Kavaliro, and it’s all thanks to you! To our incredible clients, talented contractors, and dedicated internal team—your trust, hard work, and commitment made this achievement possible. We’re deeply grateful for each of you and can’t wait to see what we’ll accomplish together in 2025! UPDATES K...

Consultants
Consultant of the Month: Benjamin Vu
We are delighted to shine the spotlight on Benjamin as our first Consultant of the Month for 2025! 🎉 Benjamin was born in the state of Utah, spent his younger years in Georgia, and currently resides in Knightdale, North Carolina. Since becoming a Project Manager back in 2011, Ben has accumulated diverse experience in industries suc...

Managed Services
All You Need to Know About Least Privilege
In IT, the principle of least privilege (PoLP) refers to the concept that any process, program or user must be provided with only the bare minimum privileges (access or permissions) needed to perform a function. For instance, if a user account has been created for accessing database records, it need not have admin rights. Also, a programmer respons...